Working flows for
governed agentic commerce.
Each use case is built, tested, and runnable in the developer demo. These are not hypotheticals — they are proved by the test suite.
An agent requests paid data from an approved merchant route. The procurement wallet checks the merchant, route fingerprint, payee, price, budget, and task binding before authorizing payment.
The mock x402 protocol simulates machine-readable payments. When approved, a DataArtifact is created and linked to the wallet, decision, and merchant route.
pnpm demo:paid-dataFlow
What it proves
Agents can participate in machine commerce without raw spending authority.
If a merchant route changes its expected payment recipient, Sovereign detects the mismatch and denies or quarantines the route. The runtime compares the current route fingerprint against the registered fingerprint for that merchant.
Quarantined routes require explicit clearance before new transactions can proceed. The quarantine event is written to the audit log.
pnpm demo:payee-driftWhat it proves
Merchant trust is not just an address allowlist. It is a continuously verified counterparty relationship.
Runtime response
PAYEE_DRIFT_DETECTED → route quarantined
Every paid data artifact is linked to the economic action that purchased it, the wallet constitution that approved it, and downstream trade plans that used it.
The provenance chain is queryable by artifact ID. It returns the full graph: merchant, route, wallet, policy version, decision packet, agent, and any downstream artifacts or trade plans that reference this data.
pnpm demo:provenanceWhat it proves
Agent memory and reasoning can be grounded in auditable economic records. Data is not just retrieved — it is receipted.
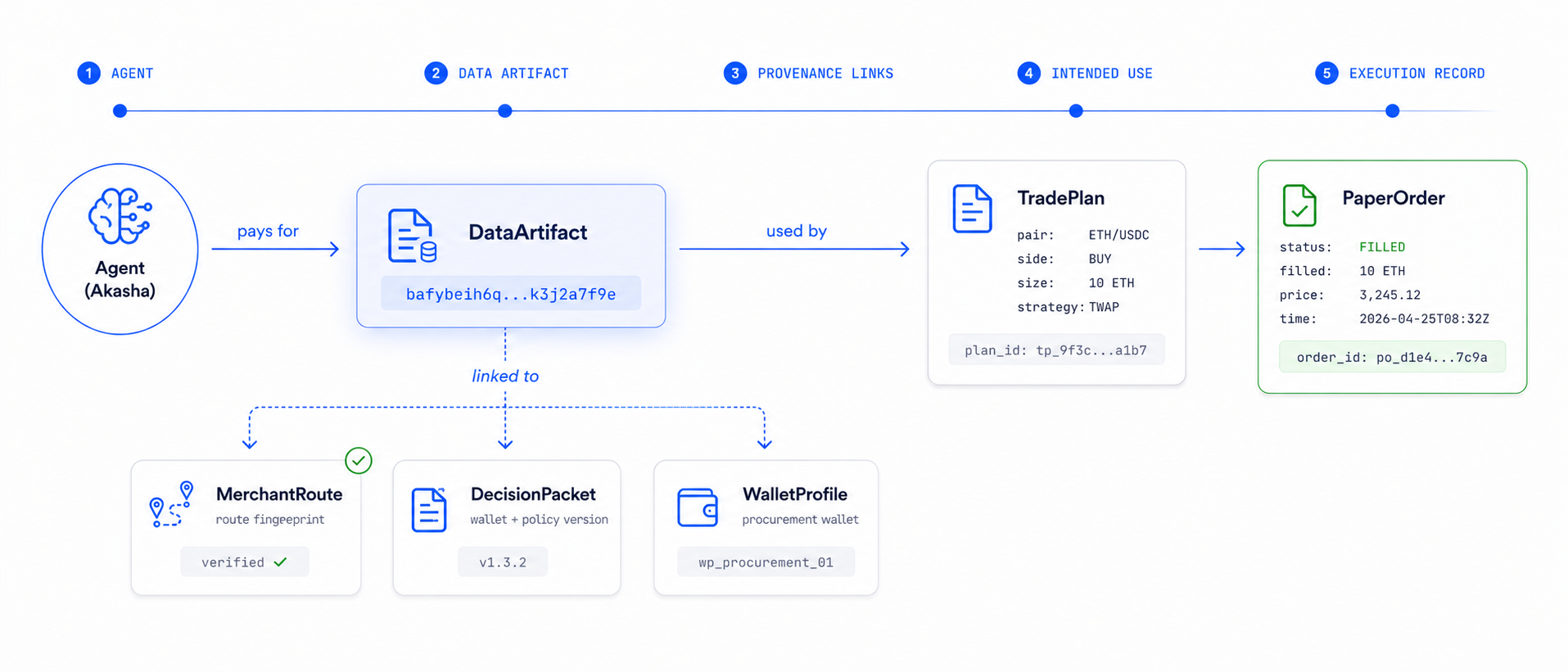
Akasha can create a trade plan from paid data, run a deterministic risk check, and request paper execution through the trading wallet.
The risk engine evaluates position size, concentration, leverage, and volatility against the wallet constitution before issuing a DecisionPacket for the paper broker. Paper orders are recorded with full audit trails.
pnpm demo:paper-tradeWhat it proves
High-risk agent behavior can be modeled, audited, and bounded before live execution is ever enabled.
Live trading is denied or escalated by default. A critical tool request cannot execute simply because the agent selected it.
The trading wallet constitution requires explicit escalation and approval before any live execution path is enabled. The denial path is fully audited.
Default response
LIVE_TRADING_DENIED → requires escalation
What it proves
The framework enables autonomy without surrendering control.
Run all five flows.
The demo scripts run each use case end-to-end and print structured output for review.