Deterministic evaluation
The runtime produces the same decision for the same input every time. No side effects during evaluation.
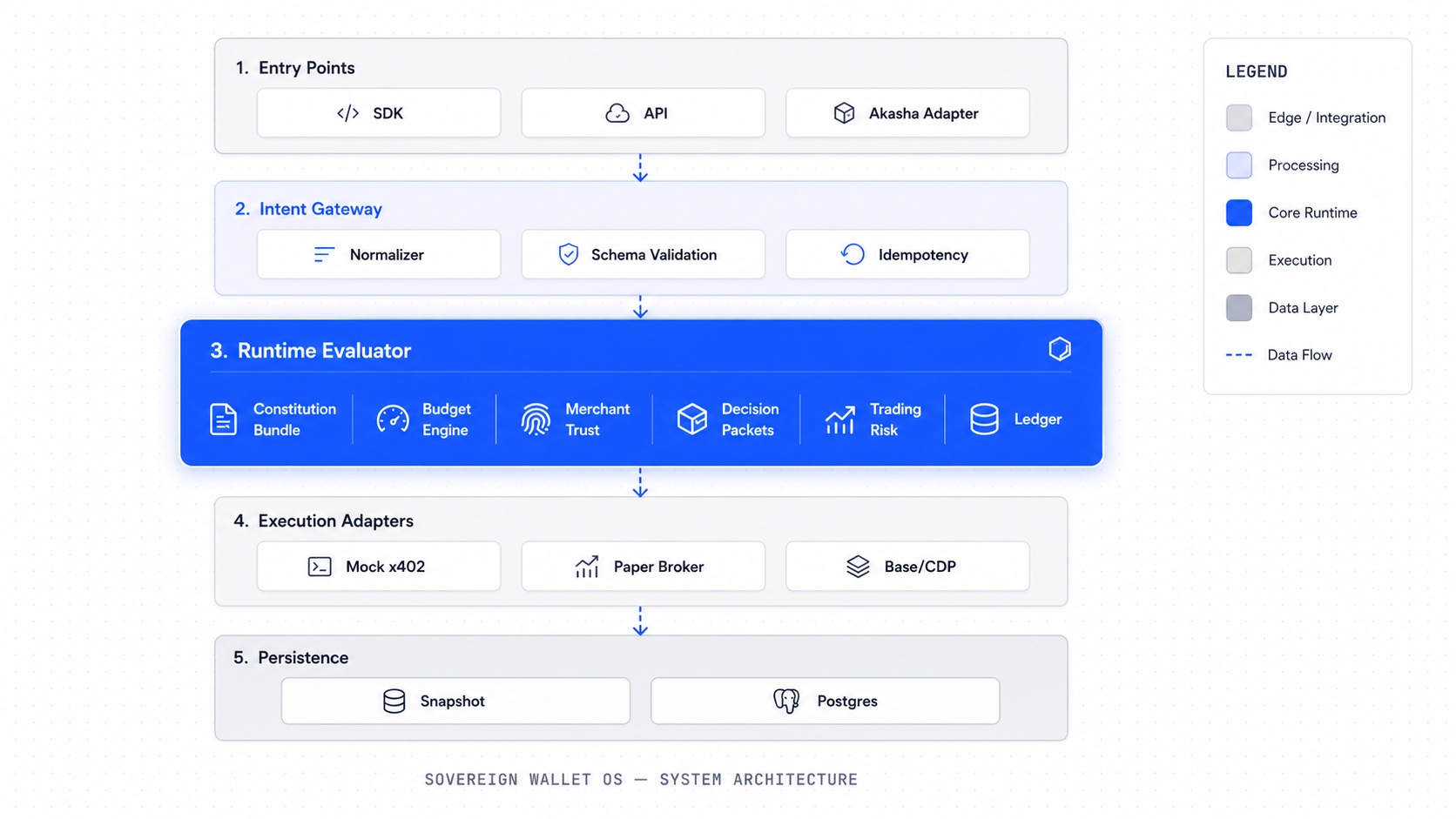
Sovereign is built as a set of composable packages, each responsible for a specific layer of the constitutional execution model.
Each layer is independently testable and depends on the layers below it.
Every x402 payment flows through the constitutional runtime before any funds move. The agent never controls the wallet.
Default mode. Full constitutional evaluation runs. No testnet payment is made. Identical constitution to Base Sepolia path.
Real x402 payment using test USDC on eip155:84532. Same constitutional path. Real settlement receipt attached to artifact.
Defined but intentionally disabled in the current MVP.
Each package owns its types, logic, and tests. No package reaches across into another layer's internals.
These are the primary types that flow through the system from intent to settlement.
| Entity | Package | Description |
|---|---|---|
| WalletInstance | domain | A wallet with type, profile, and linked constitution |
| ConstitutionVersion | constitution | Versioned policy document for a wallet |
| CompiledBundle | constitution | Executable policy derived from a ConstitutionVersion |
| EconomicIntent | domain | Typed agent request for an economic action |
| BudgetReservation | budget-engine | Hold on budget funds pending execution |
| MerchantRoute | merchant-trust | Route fingerprint and payee binding for a merchant |
| DecisionPacket | decision-packets | Scoped, signed, expiring authorization from the runtime |
| EconomicActionRecord | ledger | Settlement record for a completed economic action |
| DataArtifact | ledger | Paid data artifact with provenance metadata |
| TradePlan | trading | Agent-generated trade plan from paid data |
| RiskCheck | trading | Deterministic risk evaluation result for a trade plan |
| PaperOrder | trading | Paper execution record with status and settlement |
| PositionSnapshot | trading | Point-in-time portfolio state from paper trading |
The runtime produces the same decision for the same input every time. No side effects during evaluation.
Every layer communicates through strongly typed domain types. No untyped maps or generic objects crossing package lines.
Execution adapters are swappable. The runtime never knows which adapter will execute — it only issues packets.
The SDK has no signing surface. Agents submit intents. The runtime decides. Adapters act.
Local demos run against a snapshot file. Production-grade validation uses Postgres with schema migrations.
Audit events are append-only. No event is ever updated or deleted. The hash chain makes tampering detectable.
The SDK docs and demo runbook show the system in action.